Inference Enterprise Modeling for Insider Threat Detection Systems | GEORGE MASON UNIVERSITY
The insider threat is manifested when user behavior departs from normal compliance with established processes and policies. The motive behind this behavior may be malice or a disregard for established policies in an organization. Reliance on computers for information storage and processing, and advances in networking technology for information access/exchange have created new means and venues, and in some cases incentives, for user behaviors outside the prescribed norms. The resulting new technology challenges have made the insider threat detection even harder, especially when the threat comes from technologically savvy individuals.
Due to the variety of threats and complexity of solution methods, an organization requires employment of a wide range of procedures and technical tools since a single procedure or a single detection tool may not be enough for all types of threats and anomalies.
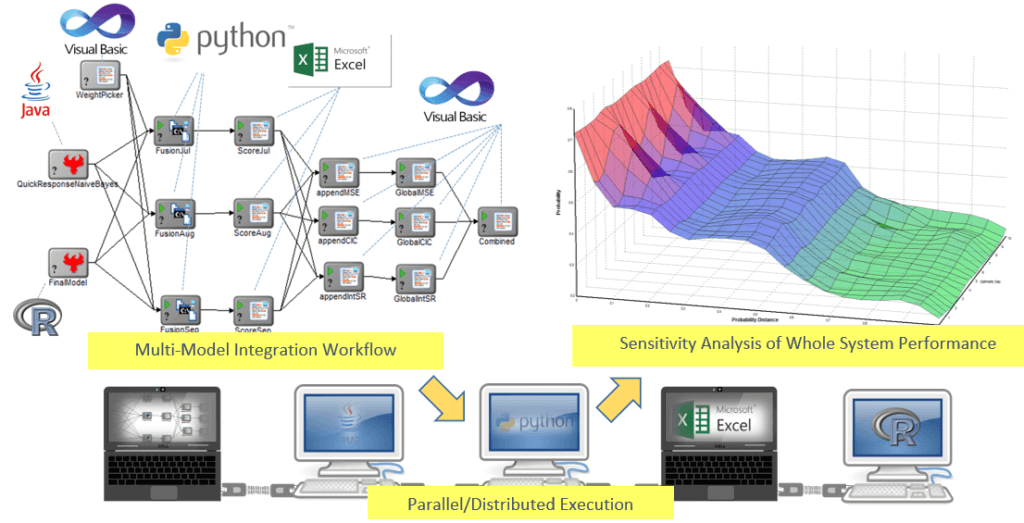
Organizations usually employ a suite of analytical models to predict the performance of the existing insider threat detection systems in their respective domains. The current practice uses a variety of different simulation and modeling formalisms and subject matter experts to address parts of the larger problem. There is a realization that complex problems cannot be solved by employing a single analytical methodology and its supporting tools; rather, they require a combination of several such methods all supplementing or complementing each other.
We use ModelCenter® to represent a given inference enterprise (information, tools, algorithms, and methods), to create an analysis workflow, and to evaluate the enterprise’s performance for a given inference task. The workflow can be instantiated with multiple data sources and different parameter values of the detection algorithms. The workflow is automated for simulating the given enterprise model. This supports analysing performance under different settings to support process reengineering. Several case studies will be shared.
Watch our free webinar right now!